The Cost of Cybersecurity Breaches
Cybersecurity breaches impose a profound financial burden on organizations of all sizes and industries. Beyond the immediate expenses of remediation and legal fees, companies face lost productivity, operational disruption, regulatory fines, and long-term damage to customer trust and brand reputation. The IBM Cost of a Data Breach Report 2025 estimates the average total cost of a single data breach to be around $4.44 million globally, reflecting an upward trend fueled by increasingly complex attacks and evolving regulatory landscapes.
Ransomware attacks, which involve malicious actors encrypting critical data and demanding payment for its release, contributed significantly to this growing financial toll. According to cybersecurity research firms, ransomware damages worldwide exceeded $20 billion in 2023, a figure that encompasses ransom payments, recovery costs, and business interruption losses.
These figures highlight an urgent need for organizations to rethink traditional defense strategies. The sheer scale and sophistication of modern cyber threats demand innovative approaches that can detect and respond to breaches swiftly and decisively. AI-powered cybersecurity, leveraging real-time data analysis and predictive capabilities, offers a promising path forward to reduce both the likelihood and impact of attacks.
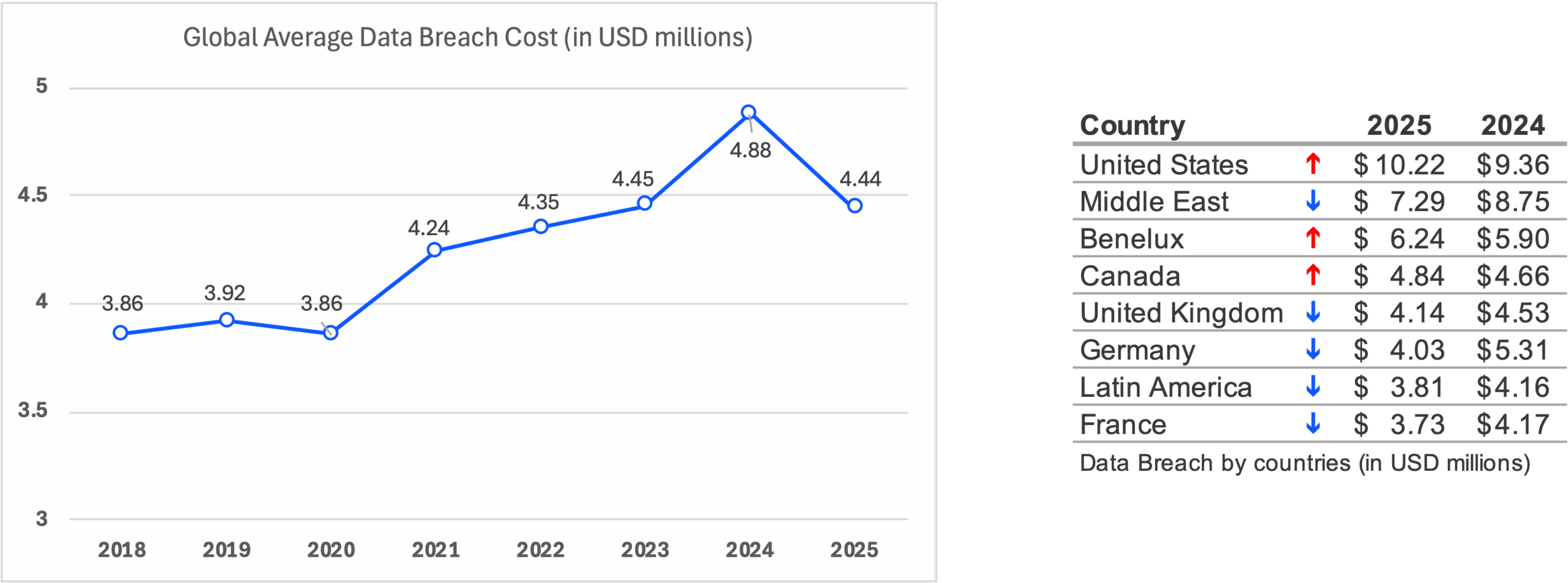
Figures from IBM Cost of a Data Breach Report 2025
The Evolution of Cyber Threats: A Changing Landscape
Cyber threats are evolving at an unprecedented pace, constantly reshaping the battleground on which organizations must defend themselves. Malicious actors no longer rely solely on simple malware or basic intrusion tactics; instead, they deploy sophisticated, multi-faceted campaigns that adapt and evolve to evade detection. These evolving methods include advanced persistent threats (APTs), fileless malware, polymorphic and metamorphic code, and increasingly, attacks powered by artificial intelligence itself.
Attackers employ a wide array of tactics, techniques, and procedures, commonly known as TTPs, to infiltrate systems, maintain persistence, and achieve their objectives. These TTPs are often tailored to specific targets, leveraging vulnerabilities unique to industries or organizations. A prime example of such sophistication is the SolarWinds supply chain attack, where malicious actors compromised a trusted software vendor’s update mechanism to infiltrate numerous organizations, bypassing traditional security controls and evading detection for months.
Furthermore, threat actors are increasingly exploiting AI-driven tools to automate attacks, analyze defenses, and craft more effective evasion techniques. This use of adversarial AI can poison machine learning models, manipulate detection algorithms, and generate malicious code that continually morphs to bypass static defenses.
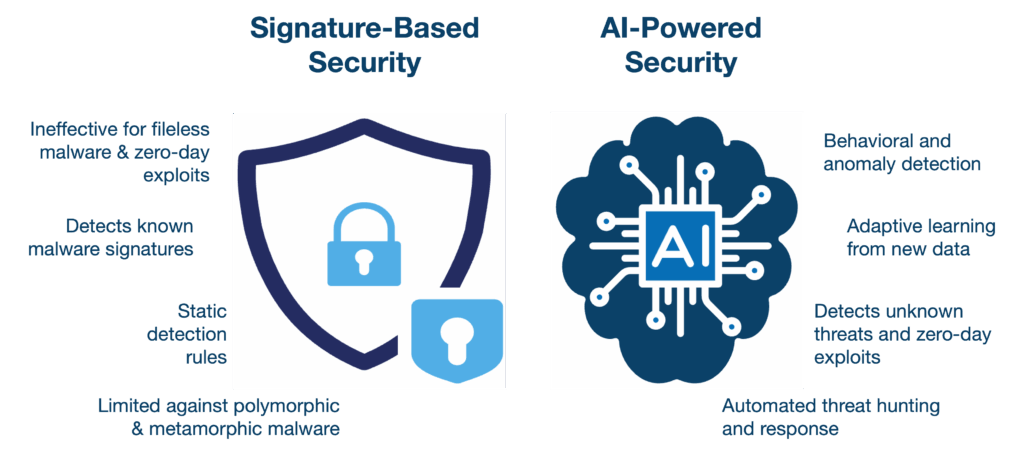
Given this rapidly changing threat landscape, cybersecurity cannot rely on reactive, signature-based methods alone. A holistic, top-to-bottom security posture that spans cloud infrastructure down to endpoints is critical. Integrating AI innovations throughout this continuum enhances detection, accelerates response, and fortifies defenses against threats that grow more complex by the day.
Why Signature-Based Security Is No Longer Enough
For many years, cybersecurity defenses relied heavily on signature-based detection methods. These traditional tools identify threats by comparing files and behaviors against a database of known malicious signatures or patterns. While effective against previously encountered malware, this approach struggles to keep pace with the rapid innovation and increasing complexity of today’s cyber threats.
Modern malware often uses polymorphism and metamorphism, continuously altering its code to avoid matching known signatures. Additionally, sophisticated attacks employ fileless techniques that reside in RAM memory or exploit legitimate system tools such as PowerShell, Windows Management Instrumentation (WMI), or the Windows Registry. These methods leave no static footprint or easily identifiable Indicators of Compromise (IOCs) for signature scanners to detect.
Consequently, relying solely on signature-based tools leaves organizations vulnerable to breaches and delayed detection. The cybersecurity landscape demands adaptive, intelligent defenses capable of analyzing sophisticated behaviors, such as unusual process executions, anomalous network traffic, and deviations from baseline system activity, rather than static patterns alone. AI-powered solutions leverage machine learning models to detect subtle indicators of malicious activity, enabling proactive threat hunting and faster incident response against zero-day exploits and APTs (advanced persistent threats).
Leveraging Cloud Computing and the AI Revolution
The rapid adoption of cloud computing combined with groundbreaking advancements in artificial intelligence (AI) is reshaping cybersecurity in profound ways. Cloud platforms offer unparalleled scalability, flexibility, and speed, enabling security solutions to be deployed quickly across diverse environments without the constraints of traditional on-premises infrastructure.
Simultaneously, recent innovations in AI, particularly the emergence of transformer models like attention mechanisms, have revolutionized machine learning capabilities. Supported by massive datasets, breakthroughs from technology giants such as Google, Microsoft, Amazon, and Apple, and accelerated by advances in high-performance computing from companies like NVIDIA, AI systems today can analyze vast streams of security-relevant data in real time.
This convergence empowers cybersecurity platforms to continuously monitor network traffic, system processes, user behaviors, microservice interactions, memory usage, and registry modifications against sophisticated baseline models of normal activity. Threats like APTs or fileless malware, which cleverly hide behind legitimate system functions, can be detected and flagged more efficiently than ever before.
Cloud-native AI-powered cybersecurity thus provides a revolutionary approach, enabling modular, scalable, and adaptive protection that can keep pace with rapidly evolving cyber threats and organizational needs.
AI-Powered Threat Detection and Response
Artificial intelligence has transformed the way cybersecurity systems detect, investigate, and respond to threats. Unlike traditional tools that rely on predefined signatures or static rules, AI-driven platforms analyze vast volumes of real-time data across endpoints, networks, and cloud environments to identify subtle anomalies and patterns indicative of malicious activity.
By continuously learning from new data, AI models build dynamic baselines of normal behavior for users, devices, and applications. This enables the detection of sophisticated threats that may otherwise remain hidden, such as insider attacks, fileless malware, and zero-day exploits. Moreover, AI accelerates incident response by automating alert triage, correlating disparate signals, and recommending or initiating containment actions swiftly, thereby reducing dwell time and limiting potential damage.
These capabilities extend beyond detection to proactive threat hunting and predictive modeling. Security teams leverage AI-powered insights to anticipate attacker tactics and develop defense strategies ahead of emerging threats. The integration of AI with cloud-based Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platforms further enhances this process by centralizing data, enabling automated workflows, and streamlining collaboration.
In essence, AI-powered threat detection and response represent a fundamental shift toward intelligent, adaptive cybersecurity that continuously evolves to meet today’s complex and fast-changing threat landscape.
Human Factors and Social Engineering: AI’s Persistent Blind Spot
While AI has dramatically advanced cybersecurity defenses, it remains limited in addressing one of the most vulnerable and exploited aspects of any organization, human behavior. Social engineering attacks, such as phishing, spear-phishing, and business email compromise, manipulate individuals into divulging sensitive information or performing actions that compromise security. These tactics exploit human psychology rather than technological vulnerabilities, making them notoriously difficult for AI systems to detect and prevent.
Despite sophisticated AI models monitoring network traffic, user behavior, and system processes, the nuances of human decision-making, trust, and error create opportunities that automated systems struggle to fully mitigate. For instance, AI can flag suspicious emails based on content or metadata but may not discern subtle contextual cues that deceive even the most cautious employees.
Addressing this blind spot requires a holistic cybersecurity strategy that combines AI-driven technology with continuous user education, awareness training, and strong organizational policies. Empowering employees to recognize and resist manipulation tactics is essential, as is fostering a culture of security mindfulness where individuals feel responsible and vigilant.
Ultimately, while AI strengthens the technical perimeter, human factors remain a critical frontier where vigilance, training, and organizational resilience must complement technological innovation.
Diverse AI Techniques Powering Cybersecurity
Artificial intelligence encompasses a variety of techniques, each bringing unique strengths to cybersecurity defenses. Understanding these methods sheds light on how AI detects and counters evolving threats.
Supervised learning involves training AI models on labeled datasets containing examples of malicious and benign activity. Common algorithms include decision trees, support vector machines, and neural networks. For instance, a supervised model might analyze email features, such as sender reputation, content keywords, and link patterns, to classify phishing attempts with high accuracy.
Unsupervised learning analyzes unlabeled data to uncover anomalies or hidden structures without predefined categories. Techniques like clustering algorithms or anomaly detection models such as isolation forests are used. For example, an unsupervised model might monitor network traffic flows, identifying unusual spikes or deviations that could indicate a stealthy intrusion or data exfiltration, even if the specific attack signature is unknown.
Neural networks excel at processing complex, high-dimensional data. Deep learning models can analyze sequences of system calls or user behaviors, detecting subtle patterns that signal advanced persistent threats or fileless malware that traditional methods miss.
Other emerging approaches like reinforcement learning enable AI systems to learn optimal defense strategies by interacting dynamically with their environment, improving automated responses over time.
Together, these AI methodologies form a layered, adaptive defense, combining pattern recognition, anomaly detection, and continuous learning, to tackle the complexity of modern cyber threats effectively.
Explainability and Trust in AI Decisions for Cybersecurity Professionals
As AI becomes increasingly integral to cybersecurity, the need for explainable and transparent AI models grows paramount. Cybersecurity professionals must understand how AI systems arrive at their conclusions to effectively interpret alerts, make informed decisions, and justify actions to stakeholders.
Explainability involves designing AI models whose decisions can be traced and rationalized, enabling analysts to distinguish between true threats and false positives. This transparency not only enhances trust but also facilitates regulatory compliance and accountability in automated security processes.
Trust in AI systems is built through consistent performance, accuracy, and clear communication of uncertainties or limitations. When cybersecurity teams can confidently rely on AI insights while retaining human oversight, they achieve a balanced partnership, leveraging AI’s speed and scale alongside human judgment and contextual understanding.
Incorporating explainable AI into cybersecurity platforms thus empowers organizations to maximize AI’s potential while managing risks associated with opaque or black-box models.
Unified Platforms and Seamless Integration
In today’s complex cybersecurity landscape, organizations benefit significantly from unified platforms that integrate multiple security functions under a single umbrella. Leading companies like Microsoft and CrowdStrike have developed comprehensive solutions that combine cloud security, endpoint protection, threat intelligence, and automated response capabilities into cohesive ecosystems.
These integrated platforms simplify management by providing centralized visibility across the entire attack surface, from cloud workloads to endpoints. They streamline workflows by automating detection, investigation, and remediation processes, often incorporating Security Orchestration, Automation, and Response (SOAR) technologies to coordinate actions across diverse security tools.
The modular nature of these platforms enables organizations to adopt tailored protection packages that fit their specific needs, scaling capabilities as threats evolve and business requirements change. This flexibility reduces complexity, lowers operational costs, and enhances overall security posture.
As the cybersecurity market grows, fueled by escalating threats and digital transformation, demand for unified, AI-enhanced platforms continues to surge. The ability to deliver integrated, cloud-native, and AI-powered security solutions is rapidly becoming a key differentiator for vendors and a critical advantage for customers.
The Market Landscape and Emerging Trends
The cybersecurity market is undergoing rapid expansion, driven by the growing frequency and sophistication of cyber threats alongside widespread digital transformation. In response, a surge of over forty companies specializing in AI-enhanced cybersecurity solutions has emerged, fueling innovation and competition.
Organizations increasingly seek unified, cloud-native platforms that provide modular, scalable, and easily deployable protections. These solutions enable businesses of all sizes to tailor defenses to their specific risk profiles without the overhead and rigidity of traditional security architectures.
However, challenges remain. The industry faces a persistent shortage of skilled cybersecurity professionals, necessitating solutions that automate routine tasks while augmenting human expertise. Additionally, the constantly evolving threat landscape demands continuous innovation to anticipate and counter novel attack vectors effectively.
Looking ahead, the integration of AI-driven threat intelligence, automation, and seamless orchestration will continue to shape cybersecurity’s future. Companies that successfully harness these technologies and deliver transparent, explainable AI solutions will be best positioned to safeguard organizations against tomorrow’s threats.
Conclusion
As cyber threats grow in complexity and scale, traditional defenses alone can no longer provide adequate protection. The integration of artificial intelligence with cloud-native architectures is revolutionizing cybersecurity, offering adaptive, intelligent, and proactive solutions that keep pace with evolving attacker tactics. While AI empowers faster detection, deeper insights, and automated responses, the human element remains indispensable, particularly in addressing social engineering and ensuring trust in AI-driven decisions.
Unified platforms that seamlessly blend cloud and endpoint security are becoming essential, providing organizations with scalable, flexible, and comprehensive protection tailored to their unique needs. Amid a rapidly expanding market and persistent talent shortages, the future of cybersecurity hinges on this symbiotic relationship between cutting-edge technology and skilled professionals.
Embracing AI-enhanced cybersecurity is no longer optional, it is imperative for organizations aiming to defend their digital assets, maintain customer trust, and thrive in an increasingly perilous cyber landscape.
